☕ Good Morning Security Gang,
Today’s show wasn’t just busy, it was one of those episodes where you can actually see the future of cybersecurity unfolding in real time.
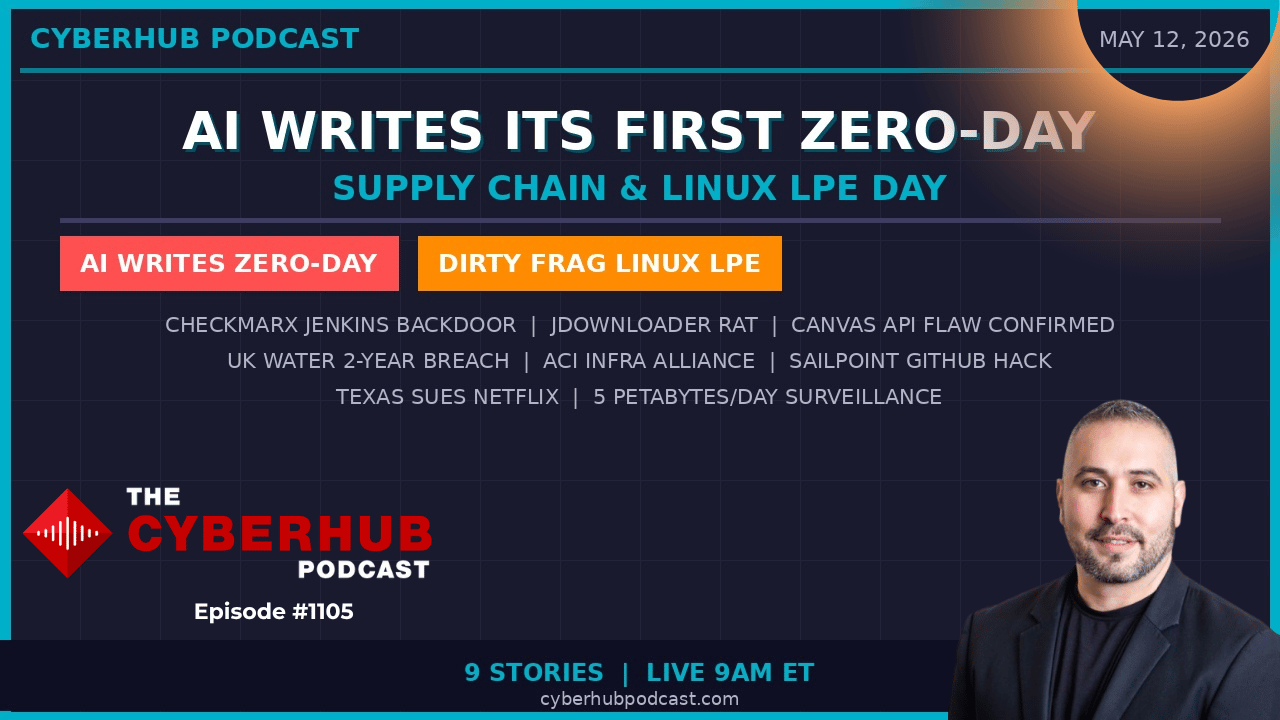
We’ve got AI autonomously building a real-world exploit, a new Linux privilege escalation flaw already seeing signs of active exploitation, a backdoored security plugin sitting inside CI/CD pipelines, a compromised official software distribution site, and a UK water utility that let attackers sit inside their network for nearly two years unnoticed.
👉 The theme today is simple and brutal:
The speed of attackers is now exceeding the operational maturity of most defenders.
Double espresso in hand, let’s get into it.
🧭 Executive Summary
Today’s threat landscape reflects a dangerous acceleration in AI-assisted offensive operations, supply chain compromise, and critical infrastructure exposure. We are now seeing AI move from supporting attackers to independently discovering and weaponizing vulnerabilities, collapsing the traditional timelines defenders once relied on.
At the same time, supply chain attacks continue targeting trusted security tooling and software repositories, while operational failures in monitoring and visibility leave critical infrastructure environments dangerously exposed. The result is a cybersecurity environment where trust assumptions, detection gaps, and slow operational response are becoming the attacker’s biggest advantage.
📰 Top Stories & Deep Dive Analysis
🤖 Google’s Big Sleep AI Creates a Real Zero-Day Exploit
This story is a watershed moment for cybersecurity.
Google’s Project Zero “Big Sleep” AI system independently discovered a memory safety vulnerability and generated a functional exploit capable of real-world use—all without human-written exploit guidance. Google responsibly disclosed the issue before public release, but the implications are massive.
For years, defenders assumed there would always be a gap between vulnerability disclosure and widespread weaponization. That assumption is now gone. AI can compress the timeline from disclosure to exploit development down to near-zero.
This fundamentally changes vulnerability management. Security teams can no longer operate under the assumption that they have days or weeks to patch critical flaws. From this point forward, organizations must behave as if every disclosed CVE already has a working exploit available on day one.
🐧 DirtyFrag – Linux Privilege Escalation Joins the “Dirty” Family
A new Linux kernel privilege escalation vulnerability dubbed “DirtyFrag” has emerged, with signs of active exploitation already underway before broad patch adoption.
Like DirtyPipe and DirtyCow before it, DirtyFrag exploits low-level kernel memory handling flaws, allowing an unprivileged user to escalate directly to root access. This is particularly dangerous because attackers only need a small foothold, a phishing payload, compromised account, or web shell—to leverage the vulnerability and gain full control.
Linux remains the backbone of cloud infrastructure, Kubernetes environments, and critical systems globally. That means exploitation here doesn’t just impact endpoints, it impacts entire production environments.
The biggest lesson is one we keep repeating: local privilege escalation flaws become devastating when combined with even minor initial access.
🔒 Checkmarx Jenkins Plugin Backdoored – Security Tools Become the Attack Path
The irony here is almost painful.
A malicious actor compromised the Checkmarx Jenkins AST plugin, a tool organizations specifically use to detect vulnerabilities inside CI/CD pipelines. The attacker inserted malicious code into the plugin itself, creating a foothold inside build environments trusted to secure production code.
This is one of the highest-leverage attacks possible in modern software development. Compromising a security tool means inheriting the trust organizations automatically extend to that platform.
The risk extends far beyond the plugin. Build secrets, signing keys, source code, and deployment artifacts may all have been exposed. Any organization using the compromised plugin should assume its CI/CD pipeline integrity has been questioned until proven otherwise.
💻 JDownloader Official Site Hacked – Trusted Downloads Become Malware
The official JDownloader website was compromised, with attackers replacing legitimate installers with trojanized versions containing a Python-based remote access Trojan.
Users who downloaded or updated the software during the compromise window unknowingly installed malware capable of:
Credential harvesting
Keylogging
Remote shell access
Persistent backdoor installation
This attack highlights a growing trend where attackers no longer rely on third-party mirrors or fake sites, they compromise the official distribution source directly.
That creates a dangerous reality: security awareness guidance telling users to “only download from the official source” is no longer sufficient by itself.
🎓 Canvas API Exploit Confirmed – 9,000 School Portals Defaced
Instructor confirmed that attackers exploited a vulnerability in the Canvas LMS portal customization API, allowing them to bypass authentication controls and deface portals across approximately 9,000 schools and universities.
This attack was not just about vandalism. It was a coordinated dual-track operation:
One track focused on stealing roughly 275 million records
The second targeted operational disruption through portal defacement and authentication failures
The operational impact was enormous. Universities canceled finals, students lost access to systems, and proctoring platforms went offline during the busiest period of the academic year.
This is a prime example of attackers maximizing leverage by combining data theft with operational chaos.
💧 UK Water Utility Breach – Attackers Sat Undetected for Two Years
South Staffordshire Water, serving 1.6 million people in the UK, was fined after attackers remained undetected inside its environment for nearly two years.
Initial access came through a phishing email in 2020. Attackers later exploited the well-known Zerologon vulnerability, left unpatched on critical domain controllers—to move laterally through the environment.
The most alarming detail? The organization’s SOC was reportedly monitoring only 5% of the environment.
“If your SOC can only see five percent of your environment, attackers already know where to hide.”
This story perfectly captures the danger of incomplete visibility. Organizations often believe they are protected because they have monitoring in place, but partial coverage creates blind spots attackers can exploit indefinitely.
And once again, water infrastructure emerges as a recurring target globally.
🏭 Private Sector Critical Infrastructure Alliance Forms
JP Morgan, AT&T, MasterCard, and Berkshire Hathaway Energy formally launched the Alliance for Critical Infrastructure, designed to fill coordination gaps left by staffing reductions and restructuring within CISA.
The alliance focuses on:
Cross-sector dependency mapping
Poly-crisis response planning
Threat intelligence coordination
Policy collaboration
This is a significant moment because it reflects the private sector recognizing that critical infrastructure resilience can no longer rely solely on government coordination. Organizations are increasingly being forced to self-organize around shared cyber risk.
🪪 SailPoint GitHub Repository Breach – Identity Platforms Become Targets
SailPoint disclosed a breach affecting one of its GitHub repositories, potentially exposing source code and integration secrets tied to enterprise identity governance deployments.
This matters because identity platforms sit at the center of enterprise trust. Understanding how privilege assignment, API integrations, and role management operate gives attackers a roadmap for targeting downstream customer environments.
This reinforces a broader trend: attackers increasingly target the vendors responsible for trust and security enforcement, because compromising them provides leverage across thousands of organizations simultaneously.
📺 Texas Sues Netflix – Privacy and Data Collection Under Fire
Texas Attorney General Ken Paxton filed suit against Netflix, alleging the company collected and monetized massive amounts of behavioral data without proper user consent.
According to the complaint, Netflix collected up to five petabytes of user behavior data daily while allegedly sharing information with advertisers and data brokers.
What makes this particularly important is the regulatory signal. States are increasingly stepping in where federal privacy legislation has stalled, creating a patchwork enforcement environment organizations must navigate carefully.
Privacy is no longer just a compliance issue, it’s becoming a direct cybersecurity and reputational risk factor.
🎯 Key Takeaway
👉 AI acceleration, supply chain compromise, and visibility gaps are redefining modern cyber risk faster than most organizations can adapt.
🛠️ Action Items for Security Leaders
🔐 Treat newly disclosed vulnerabilities as immediately exploitable
🐧 Patch Linux systems vulnerable to DirtyFrag and monitor privilege escalation activity
🔒 Audit Jenkins plugins and rotate all CI/CD secrets tied to compromised environments
💻 Validate software hashes and monitor official distribution channels for tampering
🎓 Review Canvas API access logs and confirm emergency patches are applied
💧 Expand SOC visibility and logging coverage across critical infrastructure environments
🏭 Participate in cross-sector resilience and threat intelligence initiatives
🪪 Rotate SailPoint integration tokens and audit API activity
📺 Review organizational privacy policies against actual data collection practices
🔍 Design detection strategies assuming AI-assisted attackers are already operational
🧠 James Azar’s CISOs Take
What stood out to me today is that the future we’ve been discussing theoretically is now operational reality. AI isn’t just helping attackers write phishing emails anymore, it’s autonomously discovering and weaponizing vulnerabilities. That fundamentally changes the game because it removes the human bottleneck from exploit development. Security teams that still operate on old vulnerability management timelines are going to struggle badly in this new environment.
The second takeaway is visibility. The UK water utility breach is a perfect example of how incomplete monitoring creates false confidence. A SOC monitoring five percent of the environment is not protection, it’s theater. Organizations need to stop assuming partial visibility is good enough. Because attackers only need one blind spot, and today’s threat actors are patient enough to sit inside those gaps for years.
🔥 Stay Cyber Safe.