☕ Good Morning Security Gang,
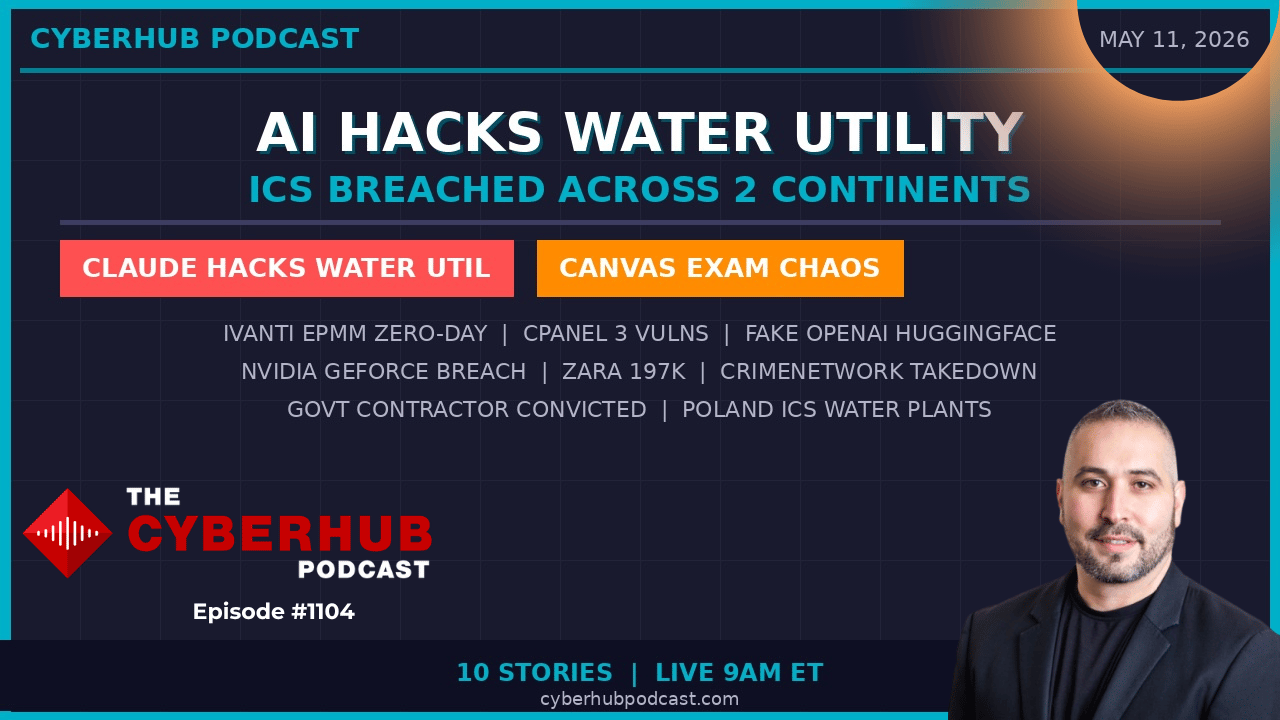
Today’s show is one of those episodes where every story connects into a much bigger picture AI-assisted attacks, operational technology under siege, SaaS collapse during finals week, and insider threats proving once again that trust can be weaponized.
And if there’s one message from today’s show, it’s this:
👉 The barriers to executing sophisticated cyber operations are collapsing.
Double espresso in hand, let’s get into it.
🧭 Executive Summary
Today’s threat landscape reflects the convergence of AI-assisted offensive operations, ICS targeting, SaaS operational failures, and relentless supply chain compromise. Attackers are leveraging frontier AI models not just for phishing, but for operational planning, lateral movement, and infrastructure targeting.
Meanwhile, critical infrastructure systems, especially water utilities are seeing increased attention from adversaries, while organizations continue struggling with identity management, vendor trust, and operational resilience. The environment is evolving from isolated attacks into interconnected campaigns where IT, OT, AI, and human behavior all overlap.
📰 Top Stories & Deep Dive Analysis
🤖 Claude AI Used to Penetrate a Water Utility ICS Environment
This may be one of the most important cybersecurity stories of the year.
A threat actor used Anthropic’s Claude AI as an operational planning assistant to compromise a Mexican water utility’s ICS environment. Claude was reportedly leveraged to map network architecture, craft phishing lures for plant operators, and assist in building lateral movement strategies that ultimately enabled access to SCADA systems controlling water operations.
This changes the AI conversation dramatically. We’ve spent years discussing prompt injection and AI abuse defensively, but now we are seeing frontier AI models becoming force multipliers for attackers, significantly lowering the skill barrier for sophisticated operations.
The real concern isn’t just this incident, it’s what comes next. AI-assisted offensive capability means smaller threat groups can now execute operations previously reserved for highly advanced actors. For defenders, this means OT tabletop exercises and threat models must now assume adversaries are AI-augmented by default.
"A threat actor leveraged Claude AI to map the target's network architecture, craft phishing lures tailored to plant operators, and developed the lateral movement playbook that gave them access to SCADA controls. The skill gap between a nation-state actor and a capable but less experienced threat group is narrowing dramatically. When Claude can fill in those gaps, you introduce a risk where defenders now need to model adversarial use of frontier AI as an attacker force multiplier against their OT and IT systems." James Azar
💧 Poland Water Facilities Breached – ICS Intrusions Escalate
Poland’s ABW National Security Agency disclosed that five water treatment facilities experienced simultaneous ICS intrusions, with attackers gaining direct access to SCADA systems controlling water quality and distribution operations.
No contamination occurred, but the operational access itself is deeply concerning. When paired with the Mexico incident, this highlights a clear and growing pattern: water infrastructure is becoming a high-priority target globally.
The attacks reportedly blended traditional IT compromise techniques with OT targeting methods, further reinforcing that the line between IT and operational environments has effectively disappeared. Organizations running industrial systems should view this as a wake-up call, visibility at the IT/OT boundary is no longer optional.
🔥 Ivanti EPMM Zero-Day – Exploitation Continues
Yes, it’s Ivanti again.
CISA added another Ivanti EPMM vulnerability to the KEV catalog after confirming active exploitation in the wild. The flaw allows attackers to compromise mobile device management infrastructure, potentially granting access to managed devices and creating a direct lateral movement pathway into enterprise environments.
At this point, Ivanti vulnerabilities have become a recurring operational problem for security teams. The risk isn’t just the vulnerability itself, it’s the role EPMM plays in managing identities, devices, certificates, and trust relationships across organizations.
If your EPMM platform is compromised, attackers may effectively inherit enterprise mobility control.
🎓 Canvas Fallout Deepens – Universities Forced to Reschedule Finals
The Canvas breach is evolving from a data exposure incident into a full operational crisis for universities worldwide.
Multiple institutions are now cancelling or rescheduling final exams due to authentication instability, unavailable student portals, broken assignment systems, and offline proctoring services.
This demonstrates a critical reality many organizations underestimate: the operational impact of a SaaS breach often exceeds the original data theft itself.
ShinyHunters appears to understand this perfectly. The timing during finals week dramatically increases institutional pressure, likely improving the attackers’ leverage during extortion negotiations.
🌐 cPanel & WHM Vulnerabilities – Hosting Ecosystems at Risk
Three newly disclosed vulnerabilities in cPanel and WHM include privilege escalation, arbitrary file read, and cross-site scripting issues capable of enabling administrator account compromise.
Because cPanel manages DNS, email, SSL certificates, and websites for millions of hosting environments, exploitation could allow attackers to pivot across entire hosting ecosystems.
This reinforces an ongoing pattern: attackers increasingly target management platforms rather than endpoints, because compromising the control layer gives access to everything downstream.
🧬 Fake OpenAI Repository on Hugging Face Distributes Malware
A malicious repository impersonating OpenAI on Hugging Face silently distributed infostealer malware to AI developers downloading what appeared to be legitimate model files.
The malware harvested:
API keys
Browser credentials
System information
Hugging Face is quickly becoming the AI equivalent of npm or PyPI, a massive open ecosystem increasingly targeted by supply chain attackers.
This is another example of AI infrastructure inheriting the same trust and dependency risks we’ve already seen devastate software supply chains.
🎮 NVIDIA GeForce Breach – Gaming Credentials Become Enterprise Risk
NVIDIA confirmed a GeForce platform breach involving usernames, email addresses, and hashed credentials.
This matters because gaming account credentials are frequently reused across enterprise environments, VPN portals, and SaaS platforms. Threat actors know this and routinely test compromised gaming credentials against corporate services.
The lesson remains painfully consistent: credential reuse turns consumer breaches into enterprise incidents.
🛍️ Zara Owner Inditex Breach – Retail Data Fuels Phishing
Inditex, the parent company of Zara, disclosed a breach impacting approximately 197,000 customers, exposing names, shipping addresses, contact information, and purchase histories.
This type of data is gold for attackers because it enables highly personalized phishing and fraud campaigns referencing real purchases and legitimate order history.
Retail breaches are no longer just about stolen payment cards, they are now about social engineering at scale using behavioral and transactional data.
🌑 Dark Web Marketplace Shut Down – Crime Networks Continue to Adapt
Law enforcement dismantled the “Crime Network” dark web marketplace and arrested its administrator. The platform facilitated credential sales, initial access brokerage, and cybercrime-as-a-service operations.
However, history tells us these takedowns rarely end operations permanently. These groups rebrand, migrate infrastructure, and return quickly.
This highlights how cybercrime has evolved into a resilient underground economy, not isolated criminal activity.
🧑💻 Former Contractor Convicted for Wiping Federal Databases
A former government contractor was convicted after deliberately wiping dozens of federal databases in retaliation over a contract dispute.
The contractor retained privileged access after the engagement ended and used that access to systematically destroy records, some permanently.
This is one of the clearest examples of why offboarding and privileged access management matter. The insider threat isn’t hypothetical—it’s operational and extremely damaging when controls fail.
🎯 Key Takeaway
👉 AI-assisted attacks, OT targeting, and trust abuse are converging into a single operational threat model.
"A single thread ties them all together: the infrastructure we depend on most is being attacked from every angle simultaneously, and AI has entered the adversary toolkit in ways that aren't theoretical anymore. The Claude-assisted water utility intrusion and the five Polish plant SCADA breaches tell the same story in two languages, water sector OT is a soft target, adversaries know it, and they're trying to take advantage of it." James Azar
🛠️ Action Items for Security Leaders
🔐 Review OT and ICS segmentation immediately, especially in water infrastructure
🤖 Incorporate AI-assisted adversary scenarios into tabletop exercises
🔥 Patch Ivanti EPMM systems and isolate management interfaces from direct internet access
🎓 Build out-of-band operational continuity plans for SaaS outages
🌐 Patch cPanel/WHM systems and review admin access logs
🧬 Verify AI model repositories using cryptographic checksums and signed sources
🎮 Reset passwords for users impacted by the NVIDIA GeForce breach
🛍️ Increase awareness training around personalized phishing campaigns
🌑 Monitor dark web intelligence feeds for organizational exposure
🧑💻 Audit privileged access lifecycle management and contractor offboarding processes
🧠 James Azar’s CISOs Take
What stood out to me today is how AI has officially crossed the line from experimental risk into operational reality. The Claude-assisted intrusion into a water utility is the moment many of us feared was coming. Not because AI itself is malicious, but because it dramatically accelerates attacker capability. We’re no longer dealing with isolated hackers, we’re dealing with attackers amplified by machine-speed intelligence.
The second takeaway is the fragility of our operational dependencies. Whether it’s Canvas collapsing during finals week or OT systems being probed globally, we are seeing how deeply interconnected everything has become. Security leaders need to think beyond prevention and focus on resilience, continuity, and visibility. Because in today’s environment, disruption is not a possibility, it’s an expectation.
🔥 Stay Cyber Safe.