☕ Good Morning Security Gang,
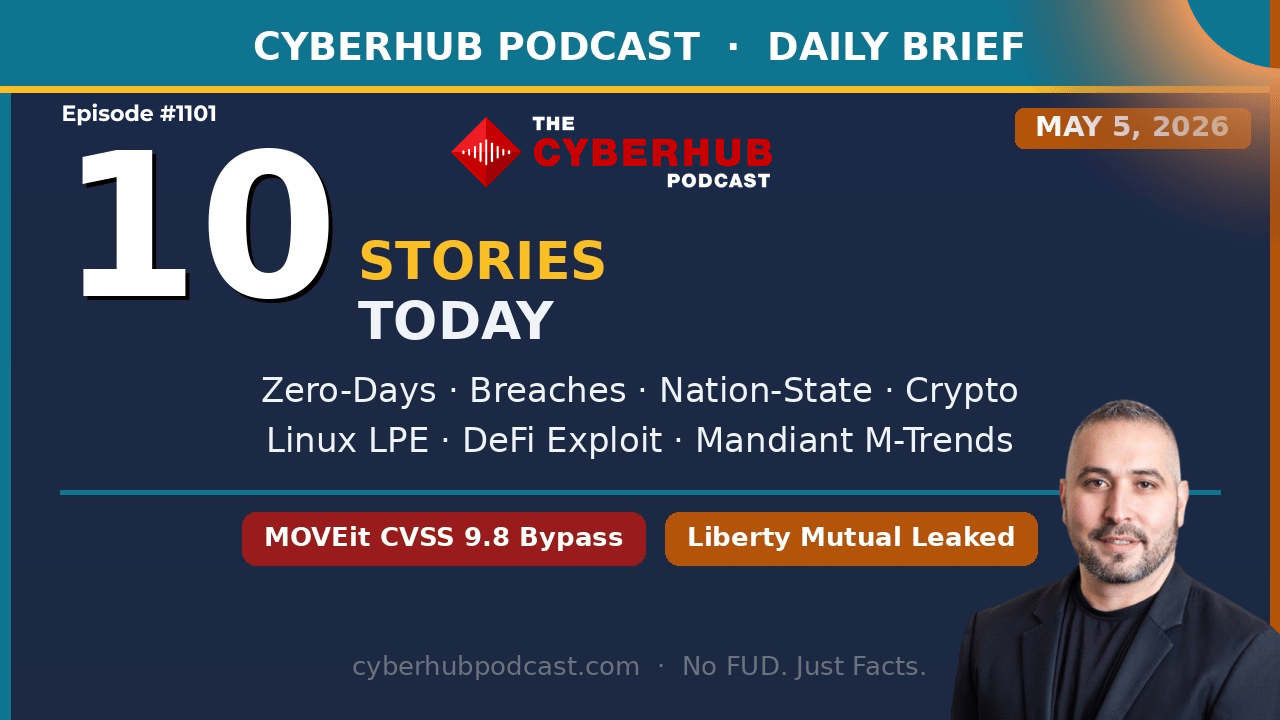
It’s Cinco de Mayo, May 5th, 2026, and today’s episode is one of those that makes you pause and rethink everything you trust in your environment.
We’re talking about MOVEit again, but this time it’s worse. We’ve got certificate trust breaking down, AWS being weaponized for phishing, Apache RCE, ransomware precursor campaigns, and even Microsoft defending cleartext password behavior.
👉 The theme today is simple: the very systems we rely on for security are now being turned against us.
Double espresso in hand, let’s get into it.
🧭 Executive Summary
Today’s stories highlight a breakdown in core trust mechanisms authentication systems, certificate authorities, cloud infrastructure, and endpoint security assumptions. Attackers are increasingly abusing legitimate platforms and trusted workflows to bypass controls, while defenders are struggling with the unintended consequences of those same trust models.
We’re also seeing continued evolution in ransomware precursor activity, supply chain exposure, and data extortion campaigns, all happening alongside a surge in cyber-enabled financial crime. The environment is no longer about perimeter defense, it’s about validating trust continuously across every layer of the stack.
📰 Top Stories & Deep Dive Analysis
🔓 MOVEit Automation Auth Bypass – Déjà Vu with Higher Stakes
A critical CVSS 9.8 authentication bypass vulnerability in MOVEit Automation allows attackers to take full administrative control without credentials. This is the same ecosystem that was mass exploited by Cl0p in 2023, and while there’s no confirmed widespread exploitation yet, history tells us exactly what’s coming.
The vulnerability enables attackers to bypass authentication entirely and chain access into sensitive workflows like payroll, financial transfers, and regulated data exchanges. Given how quickly MOVEit was exploited in the past, within 24 hours this is not a “wait and see” situation.
This is a fire drill-level vulnerability. If you’re running MOVEit Automation, you should already be patching, auditing logs, and rotating credentials. Because once exploitation starts, it won’t be gradual, it’ll be immediate and widespread.
🔏 DigiCert Breach & Microsoft Defender Failure – Trust Chain Breakdown
DigiCert’s support portal was breached via a weaponized screensaver file, leading to the issuance of fraudulent code-signing certificates used to sign malware like Zong Stealer. DigiCert revoked 60 certificates, but the situation escalated when Microsoft Defender mistakenly flagged legitimate DigiCert root certificates as malicious and removed them from systems.
This created a global trust issue where systems could no longer validate legitimate software, forcing some organizations into drastic recovery actions like OS reinstalls.
This is a rare but critical moment where both sides of the trust model failed:
The certificate authority was compromised
The endpoint protection system overcorrected
The takeaway is uncomfortable: code signing and certificate trust can no longer be assumed as reliable controls in isolation.
🏦 Everest Ransomware & Liberty Mutual – Financial Sector Pressure Campaign
The Everest ransomware group published over 100GB of data allegedly tied to Liberty Mutual, including customer information, policy data, and financial details. The breach appears linked to a third-party vendor, reinforcing the ongoing challenge of supply chain exposure.
What’s notable is the timing this comes alongside similar claims targeting financial institutions, suggesting a coordinated campaign focused on the financial sector.
Even without full confirmation of attack vectors, the pattern is clear: attackers are targeting ecosystems, not just organizations, using supply chain access to amplify impact.
☁️ AWS SES Abuse – Phishing from Inside Trusted Infrastructure
Attackers are harvesting exposed AWS IAM keys and using Amazon’s Simple Email Service (SES) to send phishing emails that pass SPF, DKIM, and DMARC checks.
Because the emails originate from Amazon infrastructure, they inherit trusted reputation and bypass traditional email filtering. The phishing pages are also hosted on AWS, creating an end-to-end attack chain within a trusted cloud provider.
This is one of the clearest examples of legitimate infrastructure abuse, where attackers don’t spoof—they operate inside the system.
The real issue here is credential hygiene. Any exposed IAM key becomes a phishing platform, turning your own environment into a threat vector.
🌐 Apache HTTP/2 RCE – Internet-Scale Exposure
A critical double-free memory corruption vulnerability in Apache HTTP Server enables remote code execution via crafted HTTP/2 requests.
With Apache powering roughly 30% of the web and HTTP/2 enabled by default, this vulnerability creates massive exposure across internet-facing systems.
Successful exploitation grants attackers access to application code, credentials, API keys, and even TLS private keys effectively compromising the entire application stack.
This is a reminder that core internet infrastructure vulnerabilities still represent some of the highest-impact risks in cybersecurity.
🧠 Venomous Helper Campaign – Ransomware Precursor in Action
A phishing campaign dubbed “Venomous Helper” has compromised over 80 organizations by deploying legitimate RMM tools like SimpleHelp and ScreenConnect.
Because these tools are trusted by EDR platforms, attackers can establish persistence and operate undetected. This is not the final stage of an attack—it’s the setup phase, often followed by ransomware deployment within 72 hours.
This highlights a critical challenge: security tools themselves can become attack vectors when abused, especially when trust-based exclusions are in place.
🔑 Microsoft Edge Password Storage – “By Design” Risk
Microsoft confirmed that Edge loads all saved passwords into memory in cleartext at browser startup and keeps them there for the duration of the session.
While labeled as “by design,” this behavior creates significant risk, especially in shared or compromised environments where attackers with elevated access can extract all stored credentials instantly.
This is a stark reminder that not all design decisions prioritize security, and organizations must compensate with additional controls like password managers and endpoint protection.
📰 MediaWorks Breach – Data Extortion Without Encryption
The WorldLeaks group published 8.5TB of data stolen from a Hungarian media company, focusing on financial records, contracts, and internal communications.
Unlike traditional ransomware, this group operates without encryption, relying purely on data theft and exposure for extortion.
This model eliminates the need for decryption keys and shifts the focus entirely to data protection and reputational risk, making backups irrelevant in these scenarios.
🚛 Cyber-Enabled Cargo Theft – Digital Meets Physical Crime
The FBI warned of a surge in cyber-enabled cargo theft, with attackers compromising logistics platforms and impersonating legitimate carriers to redirect shipments.
This represents a growing trend where cyber attacks directly impact physical supply chains, enabling theft at scale without traditional interception methods.
The implication is clear: cybersecurity is now directly tied to operational and physical risk.
📱 Facebook Phishing Campaign – Google Infrastructure Abuse
A phishing campaign targeting Facebook users leveraged Google AppSheet infrastructure to send legitimate-looking emails that bypass spam filters.
This reinforces a growing pattern where attackers use trusted platforms like Google, Microsoft, and AWS to deliver malicious content, rendering traditional domain-based filtering ineffective.
Organizations must now focus on content and behavior analysis rather than sender reputation alone.
🏆 Global Cybercrime Crackdown – $700M Seized
In a positive development, an international operation led to the arrest of 276 individuals and the seizure of over $700 million tied to cryptocurrency scam networks.
This operation disrupted large-scale fraud operations and prevented significant financial losses, demonstrating the impact of coordinated law enforcement efforts.
While encouraging, it also highlights the scale of the problem, these operations exist because they are highly profitable and resilient.
🎯 Key Takeaway
👉 Trust is being exploited at every layer, identity, infrastructure, and even security controls themselves.
🛠️ Action Items for Security Leaders
🔐 Patch MOVEit Automation immediately and audit for unauthorized access
🔏 Validate certificate trust stores and update Defender signatures
☁️ Rotate AWS IAM keys and audit SES usage for anomalies
🌐 Upgrade Apache HTTP Server to patched versions
🧠 Audit RMM tools across endpoints and remove unauthorized installations
🔑 Deploy enterprise password managers and limit browser credential storage
📰 Strengthen data protection controls to mitigate extortion risk
🚛 Secure logistics platforms and enforce MFA across supply chain systems
📩 Enhance email security with content-based detection capabilities
🏆 Monitor fraud and financial crime indicators across organizational ecosystems
🧠 James Azar’s CISOs Take
What stood out to me today is how attackers are no longer trying to break trust—they’re leveraging it. Whether it’s AWS SES for phishing, DigiCert certificates for malware signing, or RMM tools for persistence, the common thread is that attackers are operating within systems we inherently trust. That fundamentally changes how we defend, because traditional controls are built around detecting the abnormal—not the expected.
The second takeaway is that we need to rethink our security architecture around validation, not assumption. Every system, every integration, every credential needs to be continuously verified. Because in today’s environment, the question isn’t whether something is trusted—it’s whether that trust has already been compromised.
🔥 Stay Cyber Safe.