☕ Good Morning Security Gang,
Today’s episode is one of those where you step back and realize just how fast everything is evolving and breaking at the same time.
We’ve got zero-click Windows exploitation, AI pipeline RCE, supply chain compromise hitting critical developer ecosystems, a massive spike in social engineering fraud, and even a pre-Stuxnet malware discovery rewriting cyber history.
👉 The theme today is simple: automation and trust are being weaponized simultaneously.
Double espresso ready, let’s go.
🧭 Executive Summary
Today’s landscape reflects a convergence of identity abuse, developer ecosystem compromise, AI tooling risk, and large-scale financial fraud. Attackers are leveraging legitimate infrastructure, trusted platforms, and automation pipelines to operate at unprecedented speed and scale.
We’re also seeing regression in patching effectiveness, with incomplete fixes enabling zero-click exploitation, and a continued shift toward developer environments and AI pipelines as primary attack surfaces. Meanwhile, consumer fraud is reaching record levels, proving that cyber risk is no longer just enterprise, it’s societal.
📰 Top Stories & Deep Dive Analysis
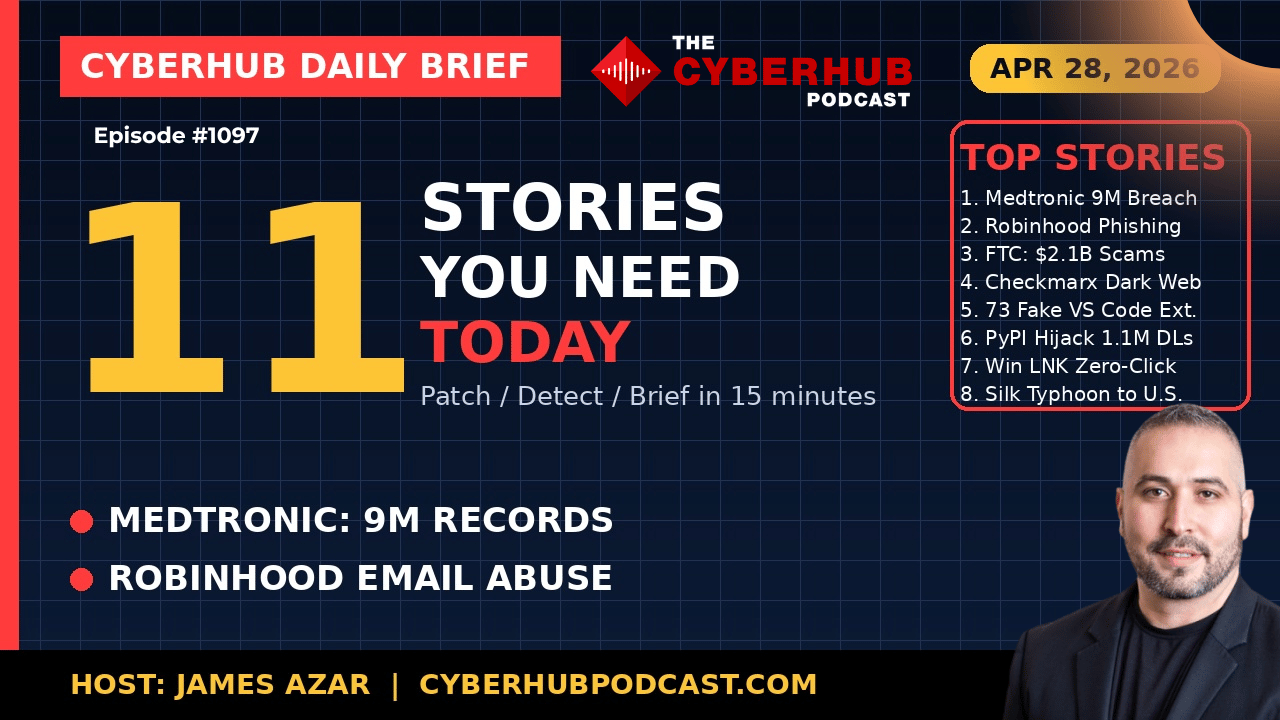
🏥 Medtronic Breach – ShinyHunters Expands the SaaS Playbook
Medtronic confirmed unauthorized access to corporate IT systems after ShinyHunters claimed over 9 million records and terabytes of internal data. The company executed its incident response plan, and the leak listing has since disappeared typically a signal of ransom negotiations or payment.
What matters here is the pattern. This aligns with previous breaches targeting SaaS ecosystems phishing identity providers and pivoting into platforms like Salesforce. Even if no medical devices or patient systems were impacted, the exposure of corporate workflows and PII creates a downstream risk for targeted phishing against healthcare providers and field engineers, expanding the blast radius beyond the initial breach.
📩 Robinhood Phishing Abuse – Legitimate Infrastructure Turned Weapon
This is one of the most creative attacks we’ve seen.
Attackers created Robinhood accounts using email variations (leveraging Gmail’s dot normalization), triggering legitimate login notifications sent from Robinhood’s own infrastructure. These emails passed all authentication checks—SPF, DKIM, DMARC, but included a malicious link embedded within user-controlled fields.
This marks a shift from spoofing to platform abuse, where attackers weaponize trusted communication channels themselves. The risk is significant because traditional email defenses are bypassed entirely making detection reliant on application-layer validation and user awareness rather than technical controls alone.
💰 $2.1 Billion Social Media Scam Surge – Cybercrime at Scale
The FTC reported that Americans lost over $2.1 billion to social media-driven scams in 2025, an eightfold increase since 2020. Investment scams alone accounted for more than half of that total.
This isn’t just a statistic, it’s a signal. Social platforms have become the primary entry point for fraud, with attackers leveraging trust, relationships, and financial pretexts to drive engagement.
The real takeaway is that cyber risk is no longer confined to enterprise systems. It’s now deeply embedded in consumer behavior, social interaction, and financial decision-making, making awareness and education just as critical as technical controls.
🔓 Checkmarx Breach Escalation – Source Code Hits the Dark Web
Checkmarx confirmed that data from its GitHub repositories, compromised during a March supply chain attack, has now been published on the dark web.
This escalation removes any ambiguity the exposure is now global and permanent. Attackers previously injected credential-stealing code into GitHub Actions workflows, meaning any environment that interacted with those pipelines may have leaked sensitive tokens or credentials.
This is a critical moment for defenders: once data is public, response shifts from containment to damage control and credential rotation at scale.
🧩 73 Malicious VS Code Extensions – Developer Layer Under Attack
Researchers identified 73 fake extensions in the Open VSX marketplace linked to the Glass Worm operation. These extensions initially appeared benign, building trust before later updates introduced malicious payloads.
The attack chain includes:
Typosquatting popular extensions
Delayed activation (“sleeper” model)
Secondary payload delivery via GitHub-hosted components
This is a direct attack on the developer ecosystem. A single compromised extension can expose source code, credentials, and SSH keys, turning a developer workstation into a high-value entry point for attackers.
🧬 PyPI Package Hijack – Supply Chain Risk in Data Engineering
The widely used “elementary-data” package (1.1M monthly downloads) was hijacked, with attackers publishing a malicious version that exfiltrated credentials, environment variables, and crypto wallets.
The attack leveraged GitHub Actions script injection to gain access, forge legitimate commits, and distribute compromised builds.
This highlights a growing trend: attackers targeting CI/CD pipelines and package registries simultaneously, enabling rapid propagation across developer environments and production systems.
🪟 Windows Zero-Click Vulnerability – Patch Regression Exploited
Akamai revealed that a recent Windows vulnerability (CVE-2026-32202) stems from an incomplete patch to a previous flaw, enabling zero-click exploitation via malicious LNK files.
Attackers can now trigger NTLM authentication or bypass security prompts simply by having the file present—no user interaction required.
This is particularly concerning because it demonstrates patch regression risk, where incomplete fixes create new attack paths. It also reinforces that patching alone is not a guarantee of security.
🤖 Gemini CLI RCE – AI Pipeline Becomes Attack Vector
A critical vulnerability in Google’s Gemini CLI allows remote code execution in CI environments by abusing trusted workspace configurations and environment variables.
In headless or automated environments, the CLI implicitly trusts local files and settings, allowing attackers to embed malicious configurations in repositories that execute upon pipeline invocation.
This turns AI tooling into a remote execution layer within CI/CD pipelines, expanding the attack surface into automated workflows that often lack human oversight.
🇨🇳 Silk Typhoon Extradition – State Actors Face Consequences
A suspected Chinese cyber operative linked to Silk Typhoon was extradited to the U.S., facing charges tied to the mass exploitation of Microsoft Exchange vulnerabilities.
This marks a rare but significant development in holding state-aligned actors accountable. While it may not deter all activity, it signals increasing willingness to pursue legal action against cyber operators globally.
🧠 Pre-Stuxnet Malware Discovery – Cyber Warfare Started Earlier Than We Thought
SentinelLabs uncovered a malware strain predating Stuxnet by at least five years, targeting engineering and simulation platforms used in nuclear research.
This discovery rewrites the timeline of cyber warfare, showing that sophisticated sabotage capabilities existed as early as 2005.
The implication is profound: cyber operations as strategic tools have been evolving far longer than most organizations have been defending against them.
🛠️ Action Items for Security Leaders
🔐 Rotate all credentials tied to Checkmarx and compromised CI pipelines
📩 Audit transactional email templates for user-controlled input injection
🧩 Restrict developer environments to approved extensions and package sources
🧬 Pin and verify all dependencies in npm and PyPI ecosystems
🪟 Apply Windows patches and monitor for abnormal NTLM authentication activity
🤖 Secure AI tooling in CI/CD pipelines and restrict environment trust boundaries
💰 Implement organization-wide awareness training on social media scams
🔍 Monitor SaaS platforms for phishing-based identity compromise patterns
📊 Enhance detection for OAuth abuse and API-based data exfiltration
🌍 Incorporate geopolitical cyber activity into risk modeling and response plans
🧠 James Azar’s CISOs Take
What stood out to me today is how attackers are leveraging trust at every level from email infrastructure to developer tools to AI pipelines. We’ve spent years building systems to automate and simplify workflows, but in doing so, we’ve also created pathways that attackers can exploit with minimal friction. The Robinhood case and the Gemini CLI vulnerability are perfect examples of how legitimate systems can be turned into attack vectors.
The second takeaway is speed. Supply chain attacks, phishing campaigns, and fraud operations are all happening faster than ever before. By the time we detect an issue, attackers have already pivoted, propagated, and monetized. That means our defenses need to evolve not just to prevent compromise, but to detect and respond in near real time. Because in this environment, the organizations that can’t keep up won’t just fall behind, they’ll become targets.
🔥 Stay Cyber Safe.