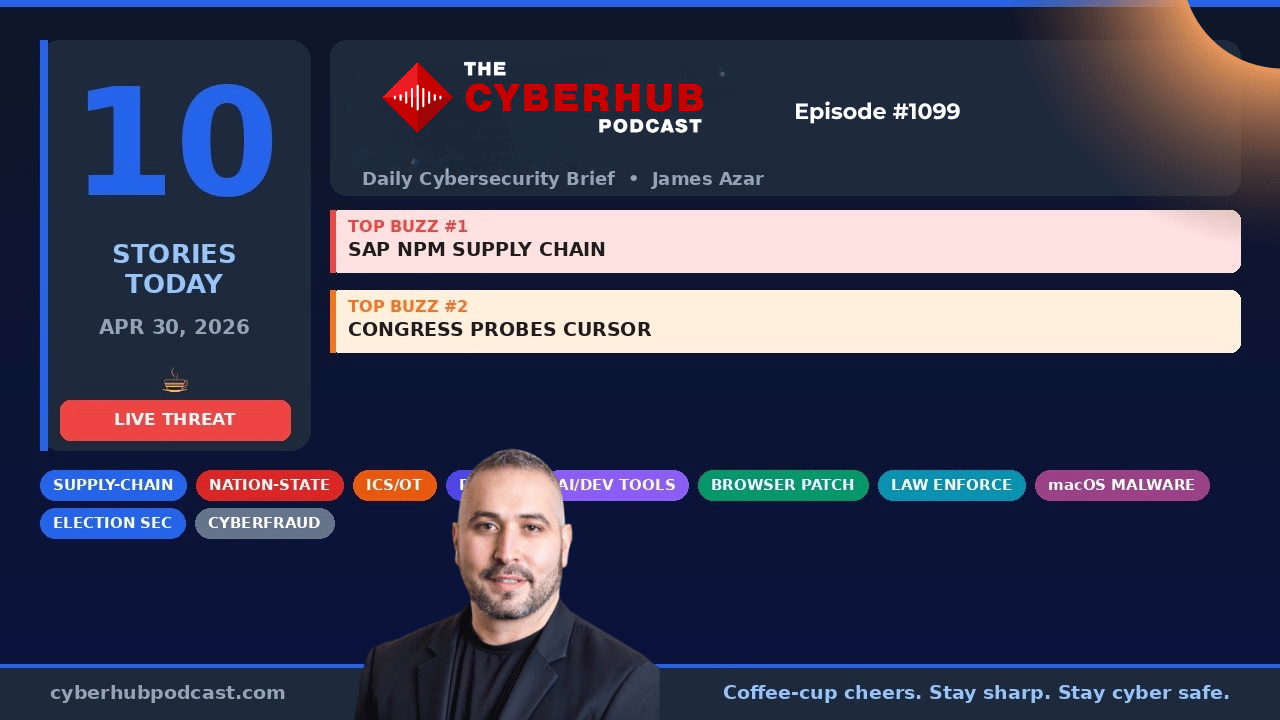
☕ Good Morning Security Gang,
Today’s episode is one of those where you can feel the pressure building across every layer of cybersecurity from supply chain attacks to critical infrastructure exposure to geopolitical cyber threats.
If there’s one theme across everything we covered today, it’s this:
👉 Attackers are moving faster than our ability to detect, respond, and even patch.
Double espresso in hand, let’s get into it.
🧭 Executive Summary
Today’s show highlights a dangerous acceleration in supply chain compromise, infrastructure exploitation, and nation-state cyber activity. We’re seeing attackers weaponize CI/CD pipelines, exploit authentication systems before patches are even deployed, and target both critical infrastructure and democratic institutions.
At the same time, AI tooling and geopolitical tensions are converging, creating a landscape where technical risk, human targeting, and policy decisions are colliding in real time. The takeaway is clear: security teams must operate at attacker speed or risk falling behind.
📰 Top Stories & Deep Dive Analysis
🧬 SAP npm Supply Chain Attack – CI/CD Pipelines Compromised in Real Time
Four official SAP npm packages were compromised in a supply chain attack dubbed “Mini Shehulud,” where attackers embedded a malicious pre-install script that executed automatically when pulled into CI/CD pipelines. The payload silently exfiltrated GitHub tokens, npm credentials, cloud provider secrets (AWS, Azure, GCP), and Kubernetes configurations.
What makes this attack particularly dangerous is its automation. The moment a pipeline pulled the infected package, the compromise was complete no user interaction required. The stolen data was even pushed into attacker-controlled GitHub repositories, signaling a highly organized and repeatable attack model.
This is supply chain compromise at machine speed. One infected dependency can cascade across thousands of environments within minutes, turning developer pipelines into mass credential exfiltration engines.
🔓 cPanel Authentication Bypass – Exploited Before Disclosure
A critical authentication bypass vulnerability in cPanel and WHM was actively exploited in the wild before the official advisory and patch were released. Hosting providers globally responded by blocking access ports at the network level while racing to deploy fixes.
This vulnerability is particularly impactful because of cPanel’s role as a multi-tenant hosting control plane. A single compromised instance can grant attackers access to websites, databases, email servers, and administrative controls across multiple customers.
The most concerning aspect here is timing—attackers were already exploiting the flaw before defenders even knew it existed, reinforcing the growing trend of pre-disclosure exploitation and shrinking response windows.
🏭 OT Exposure – Hundreds of Critical Systems Accessible Without Authentication
Forescout identified over 600 industrial control system (ICS) and operational technology (OT) panels exposed via unauthenticated VNC access, with nearly 60,000 VNC servers globally lacking proper authentication.
These systems span energy, water, manufacturing, and government environments, meaning exploitation could have direct physical consequences. Attackers don’t need advanced exploits here—just access.
This is a stark reminder that basic security hygiene failures in OT environments can create nation-state-level risks, especially as these systems remain connected to the internet without proper safeguards.
🌐 Browser Security Updates – Critical Vulnerabilities Require Immediate Action
Both Chrome and Firefox released patches addressing critical vulnerabilities, including memory safety issues and use-after-free bugs that could allow remote code execution or data disclosure.
While these updates may seem routine, they are not optional. Browsers remain one of the most exposed attack surfaces in any organization, and delayed patching can provide attackers with an easy foothold into enterprise environments.
This is a reminder that endpoint hygiene is still one of the most effective defensive measures available.
🤖 Cursor AI RCE – Developer Workstations Become Entry Points
A critical vulnerability in Cursor AI allows attackers to achieve remote code execution simply by convincing a developer to clone a malicious repository. The exploit leverages pre-commit hooks that execute automatically during routine operations.
This transforms developer environments into high-value targets. Once compromised, attackers can access source code, API keys, and infrastructure credentials, effectively pivoting into broader enterprise systems.
The risk here extends beyond the vulnerability itself, it’s the combination of automation, trust, and developer behavior, which together create a powerful attack vector.
🇨🇳 AI Supply Chain Scrutiny – Congress Investigates Chinese Model Usage
U.S. lawmakers are investigating companies using AI models developed in China, raising concerns about data exposure, censorship, and intellectual property risks.
This marks a shift where AI is no longer just a technology issue, it’s a national security concern. Organizations must now consider not just performance and cost, but also geopolitical risk when selecting AI vendors.
Expect increased regulation and scrutiny in this space as governments seek to control the flow of sensitive data and protect domestic innovation.
🇮🇷 Iranian Psychological Cyber Operations – Targeting U.S. Personnel
An Iran-linked group conducted a psychological operation by sending threatening messages via WhatsApp to U.S. military personnel and publishing personal data of service members.
While not a direct system compromise, this represents a form of information warfare designed to intimidate and destabilize. These operations blur the line between cyber and psychological tactics, expanding the definition of cyber threats beyond traditional technical attacks.
This is a reminder that cyber conflict is not just about systems, it’s about people and perception.
👮 Black Axe Arrests – Disrupting Organized Cybercrime
European authorities arrested ten members of the Black Axe cybercrime network, known for large-scale financial fraud, romance scams, and money laundering operations.
This highlights the industrialization of cybercrime, where organized groups operate like businesses with structured roles and global reach. While arrests are a positive step, these networks are resilient and often quickly rebuild.
The broader takeaway is that cybercrime is now a mature, global industry, requiring coordinated international responses.
🗳️ Election Security Warning – Midterms in the Crosshairs
The head of U.S. Cyber Command and the NSA warned that foreign adversaries are expected to target the 2026 midterm elections. At the same time, concerns were raised about reduced federal support for election security initiatives.
This creates a potential gap in coordination between federal, state, and local entities responsible for protecting election infrastructure. As adversaries continue to refine their tactics, this fragmentation could increase risk.
This is not a hypothetical scenario, it’s a known and anticipated threat, requiring proactive preparation across all levels of government.
🛠️ Action Items for Security Leaders
🔐 Audit and rotate all credentials exposed through SAP npm packages immediately
💻 Patch cPanel systems and review logs for unauthorized access attempts
🏭 Remove unauthenticated VNC access from all OT and ICS environments
🌐 Push Chrome and Firefox updates across all endpoints without delay
🤖 Restrict AI development tools and audit repository sources before cloning
🧩 Evaluate AI vendor supply chains for geopolitical and data risk
🧠 Train personnel on social engineering and psychological cyber tactics
👮 Monitor for financial fraud indicators tied to organized cybercrime groups
🗳️ Strengthen election security coordination across state and local systems
📊 Align detection and response capabilities with faster attack timelines
🧠 James Azar’s CISOs Take
What stood out to me today is how quickly attackers are moving. Whether it’s the SAP supply chain attack or the cPanel vulnerability, the pattern is the same exploitation is happening before organizations even know there’s a problem. That fundamentally changes how we need to think about defense. It’s no longer about reacting quickly, it’s about anticipating where the next attack will happen and closing those gaps before they’re exploited.
The second takeaway is the convergence of cyber and geopolitical risk. From AI supply chain concerns to election security warnings, cybersecurity is now deeply tied to national security and global stability. As CISOs, we’re not just protecting systems anymore, we’re part of a much larger ecosystem that includes policy, economics, and human behavior. And that means our role is only going to get more complex from here.
🔥 Stay Cyber Safe.